Last updated at Tue, 16 Jan 2024 16:23:00 GMT
While wandering through the dark alleys of the Internet we encountered an unusual malware artifact, something that we never observed before that gave us fun while we meticulously dissected it until late night.
The more we spent time looking at it, the more it started to look unusually familiar. As a matter of fact it turned out being the exact same botnet that an audacious Reddit user of possible German origin named “throwaway236236” described in a very popular I Am A thread you can read here.
Following is an overview of this malware labelled by the creator as Skynet: a Tor-powered trojan with DDoS, Bitcoin mining and Banking capabilities, that we observed spreading through the veins of Usenet.
Beware the warez
“People download software from Usenet and install it in the offices or at friends pretty often. Also Usenet isn't that hard anymore, as easy as buying a premium account for an onc click hoster. Most Providers have their own Usenet client for idiot proof downloads”
- throwaway236236
Usenet is a distributed discussion platform established around 1980 and still very popular worldwide.
Despite its original intent of simply being a plain text discussion forum (much like bulletin boards), over the years it has become a widely adopted platform for distributing pirated content such as movies and games, which are generally uploaded as RAR archives then split into chunks to circumvent the size limitations of Usenet's protocol.
Consequently and inevitably, malware writers found a perfect vehicle in Usenet for spreading viruses, just like what happened to other file sharing networks such as eDonkey, Gnutella and BitTorrent.
Today, Usenet has become a malware minefield.
The security industry seems to have its unblinking eye focused on the evolution of more fashionable, and possibly more widespread, infection vectors such as exploit kits and other traditional products of the Russian blackmarket. In the meantime, part of the underground keeps distributing their malware almost unnoticed through alternative channels, such as file sharing. As a matter of fact, this botnet appears to have slid under the radar for quite some time now.
Ironically, spreading malware through file sharing is still quite effective:
- There's no need to exploit the victims, they're going to directly execute the malware.
- The file shares are very easy to employ.
- They are hard to eradicate.
- They have a large pool of potential victims.
The only pitfall is that they require some social engineering component, ie, luring the victims to download the trojaned files, but that's the case for most attack vectors in today's world.
Malware Overview
“I operate a ~10k botnet using a ZeuS software I modified myself, including IRC, DDoS and bitcoin mining. Everything operating tru TOR hidden service so no feds will take my servers down.”
- throwaway236236
The malware sample we retrieved from Usenet has an unusually large size (almost 15MB) and has a fairly low detection rate (7/42).
It was not observed on VirusTotal and apparently it was not observed on any other online resource before our discovery.
The core code base composes a very simple Tor-enabled IRC bot which incorporates DDoS and a few other capabilities. A large part of the binary appears to be junk data, possibly to better disguise it as a legitimate download. It also empowers several obfuscation routines to twist detection.
The malware comes along with 4 additional embedded resources:
- A ZeuS bot.
- The Tor client for Windows.
- The CGMiner bitcoin mining tool.
- A copy of OpenCL.dll, used by CGMiner for CPU and GPU hash cracking.
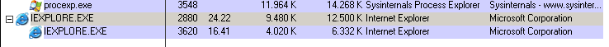
When executed, the malware first copies itself in a randomized directory under %AppData% and then starts an initialization routine that consists of several process creations and injections, resulting in the end with the core being disguised either as Internet Explorer or as svchost.exe:
In order to initialize its components, the malware creates multiple legitimate processes in suspended state, overwrites their memory with the desired malicious executables and resumes their execution.
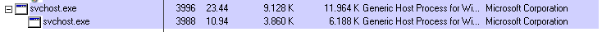
From the command line arguments we can guess that the malware does not only use Tor to connect to its backend infrastructure but also creates a Tor Hidden Service on the infected system itself:
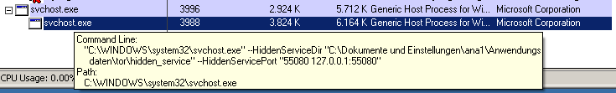
In order to enforce execution after reboot, it creates a traditional entry in the Run registry key:
Torify all the things!
“TOR is pretty safe as long as you don't use exit nodes, which I never do, because everything is inside hidden services. Hidden Service guarantees the traffic is only readable at the actual server, the magic of private/public key encryption.”
- throwaway236236
For those of you that might not be as familiar, Tor is an anonymity network operated by volunteers which provides encryption and identity protection capabilities. Tor is a great initiative that helps people all over the world protect themsleves from surveillance and traffic interception as well as circumvent Internet censorship: it's widely used by whistleblowers, political activists, and anyone concerned about the privacy and safety of their communications.
At the same time though, it does get abused a lot, which we also describe in this article. However, this article is not condemning the network as it's legitimate use is still a very valuable service.
The potential use of Tor as a bulletproof botnet infrastructure has been discussed several times in the past (for example at Defcon 18 by Dennis Brown), but we have never observed it being implemented in a real case scenario before. In September the German Antivirus vendor G-Data briefly described a similar case, which we believe could probably belong to the same malware family.
Common botnets generally host their Command & Control (C&C) infrastructure on hacked, bought or rented servers, possibly registering domains to resolve the IP addresses of their servers. This approach exposes the botnet from being taken down or hijacked. The security industry generally will try to take the C&C servers offline and/or takeover the associated domains by making them point to a different host by cooperating with hosting providers and domain registrars (this practice is commonly known as “sinkholing”), effectively disrupting the botnet's operations.
In some cases these efforts are nullified when the botnet operators acquire some services from a particular type of hosting provider that guarantees the operators that they won't respond to abuse complaints nor cooperate with takedown requests. These providers are commonly known as “bulletproof hosting” and they are widely used in the cybercrime ecosystem. However their services are typically more expensive and they might not be 100% reliable.
What the Skynet botnet creator realized, is that he could build a much stronger infrastructure at no cost just by utilizing Tor as the internal communication protocol, and by using the Hidden Services functionality that Tor provides.
Hidden Services are a functionality of the Tor network introduced in 2004 that permits the creation of completely anonymous and concealed services accessible through Tor only (or through a bridge like Tor2Web). These hidden servers publicize their existence through Tor using a public encryption key which is then indexed in Tor's directory servers. Out of the keys generated for the service, a .onion pseudo-domain is generated, which will then be used to resolve and contact the hidden server. At no point is the original IP address of the hidden server disclosed, nor do the directory servers know the identity that is behind a .onion domain. There is no way to identify the origin of the hidden service and neither to revoke or take over the associated .onion domain. Details on the implementation of Tor Hidden Services can be found here.
Skynet runs all its C&C servers as Hidden Services and all compromised computers are configured to be part of the Tor network as well.
The advantages of this approach are:
- The botnet traffic is encrypted, which helps prevent detection by network monitors.
- By running as an Hidden Service, the origin, location, and nature of the C&C are concealed and therefore not exposed to possible takedowns. In addition, since Hidden Services do not rely on public-facing IP addresses, they can be hosted behind firewalls or NAT-enabled devices such as home computers.
- Hidden Services provide a Tor-specific .onion pseudo top-level domain, which is not exposed to possible sinkholing.
- The operator can easily move around the C&C servers just by re-using the generated private key for the Hidden Service.
Long story short, Tor, due to its design and internal mechanics, makes it a perfect protocol for botnets. Because of this, all critical communications of Skynet to its C&C servers are tunneled through a Tor SOCKS proxy running locally on compromised computers.
Following are all the hardcoded .onion pseudo-domains we were able to identify, we observed only some of them being actively used:
6ceyqong6nxy7hwp.onion
owbm3sjqdnndmydf.onion
4njzp3wzi6leo772.onion
qdzjxwujdtxrjkrz.onion
x3wyzqg6cfbqrwht.onion
niazgxzlrbpevgvq.onion
ua4ttfm47jt32igm.onion
6tkpktox73usm5vq.onion
4bx2tfgsctov65ch.onion
gpt2u5hhaqvmnwhr.onion
7wuwk3aybq5z73m7.onion
742yhnr32ntzhx3f.onion
f2ylgv2jochpzm4c.onion
6m7m4bsdbzsflego.onion
xvauhzlpkirnzghg.onion
h266x4kmvmpdfalv.onion
jr6t4gi4k2vpry5c.onion
ceif2rmdoput3wjh.onion
uzvyltfdj37rhqfy.onion
uy5t7cus7dptkchs.onion
As mentioned, the malware also creates a Tor Hidden Service on every compromised computer on port 55080. Nothing is listening on such port by default, but when the operator issue a particular command on the IRC C&C, the malware will open a SOCKS proxy on port 55080 which will then be reachable through a newly created .onion domain.
IRC Botnet like it's 1999
“DDoS is only useful for trolling, best applied when two companies sue each other accusing use of DDoS in competition.”
- throwaway236236
The core of the malware provides functionalities that can be operated through specific commands submitted through the IRC channels the bot connects to. When it comes to DDoS, the malware includes support for SYN flooding, UDP flooding, Slowloris flooding, and a generic HTTP flooding.
As previously said, the malware connects to an IRC server hosted behind a Tor Hidden Service and use the following nickname pattern:
[NED-XP-687126]USERNAME
You can find it also in a screenshot throwaway236236 provided himself on the Reddit thread:
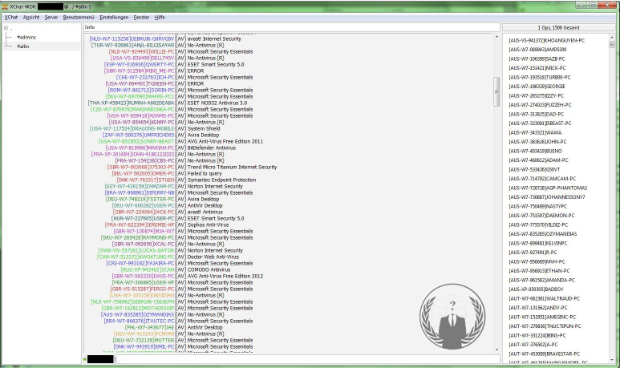
Following is a list of commands that can be used to execute specific functions of the bot.
| Feature | Commands |
|---|---|
| Get information on the compromised computer | !info, !version, !hardware, !idle |
| Download and execute files | !download |
| Download a binary to memory and inject it into other processes | !download.mem |
| Visit a webpage | !visit, !visit.post |
| SYN and UDP flooding | !syn, !syn.stop, !udp, !udp.stop |
| Slowloris flooding | !slowloris, !slowloris.stop |
| HTTP flooding | !http.bwrape, !http.bwrape.stop |
| Open a SOCKS proxy | !socks |
| Retrieve .onion address of the Hidden Service opened on the compromised computer | !ip |
We managed to patch and hijack the malware and make it connect to an IRC server hosted behind a Tor Hidden Service that we created uniquely for testing purposes. We started playing with it to try its functions, and here are some log examples from our tests.
Retrieve generic information on the compromised computer:
<claudio> !info
<[DEU-XP-625287]ANALYST> [AV: No-Antivirus (R)] [GPU: VirtualBox Graphics Adapter] [MEM: 1023 MB] [HASHES: 0.00 MH/s] [IDLE: 0 sec]
Retrieve details on hardware available:
<claudio> !hardware
<[DEU-XP-625287]ANALYST> [HW] GPU: VirtualBox Graphics Adapter MEM: 1023 MB
Retrieve the version of the malware installed:
<claudio> !version
<[DEU-XP-625287]ANALYST> [VER] Skynet_0.4
Check idle time:
<claudio> !idle
<[DEU-XP-625287]ANALYST> [IDLE] I'm idle for 0 seconds.
Start a SYN flooding DDoS attack:
<claudio> !syn <TEST IP> 80 1 60
<[DEU-XP-625287]ANALYST> [SYN] Started flooding <TEST IP>
Stop an ongoing attack:
<mark> !syn.stop
<[DEU-XP-625287]ANALYST> [SYN] Stopping <TEST IP>
Start a Slowloris flooding attack:
<claudio> !slowloris
<[DEU-XP-625287]ANALYST> [SL] Failed to start!, missing parameters: [DNS] [PORT] [HOLD_DELAY] [TIME in sec] [SOCKETS]
Start a generic HTTP flooding attack:
<claudio> !http.bwrape
<[DEU-XP-625287]ANALYST> [HTTPBW] Failed to start!, missing parameters: [URL] [SIZE] [TIME]
Start a SOCKS proxy behind a Tor Hidden Service on the compromised computer:
<claudio> !socks on
<[DEU-XP-625287]ANALYST> [SOCKS] Started
Retrieve the .onion domain pointing to the proxy just opened.
<mark> !ip
<[DEU-XP-625287]ANALYST> [HS] t3svp5x674d7qqxh.onion
ZeuS
“Got around 1k Liberty Reserve $ for random zeus logs and million email adresses I found in a shop.”
- throwaway236236
As mentioned by the creator on the Reddit post, ZeuS, an extremely common Banking Trojan whose source code has been leaked some time ago, represents a core part of the botnet and probably the main source of income from this malicious infrastructure. The leak of said source code also led to some variants, including the more recently discovered Ice IX and Citadel bots. The operator kindly provided a screenshot of his ZeuS control panel on Reddit as well:
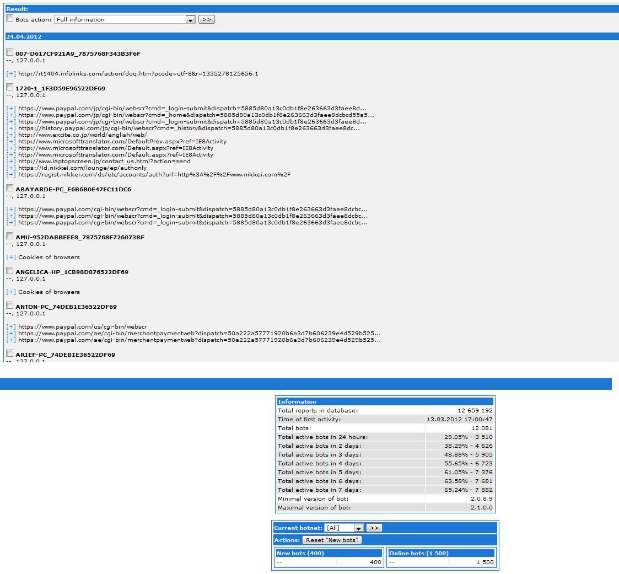
In this particular case, the malware is provided with a ZeuS bot embedded into the resource with ID 5000. Despite the claims of being largely modified, the bot shows some traditional behavior without any peculiar apparent changes.
It has a decent average Antivirus detection (36/46).
Just as the IRC C&C server, also the ZeuS C&C server is hosted behind a Tor Hidden Service.
When executed, it tries to fetch an updated configuration from:
hxxp://localhost:42349/z/config.bin
In a traditional ZeuS botnet, the address for the configuration updates would be an external public server, while in this case it's requesting them to a proxy running locally on the compromised computer on port 42349. This proxy then translates the request to a specific Tor .onion pseudo-domain and tunnel the requests through the Tor SOCKS proxy listening on port 9050.
We managed to extract such domain and as expected, the translated configuration URL is the following:
hxxp://qdzjxwujdtxrjkrz.onion:80/z/config.bin
At the same address we can find the landing page which ZeuS uses to report the harvested credentials:
hxxp://qdzjxwujdtxrjkrz.onion:80/z/gate.php
Following is the decoded updated configuration in XML format that we retrieved at the time of writing:
<?xml version="1.0" encoding="ISO-8859-1" ?>
<root>
<zeusbuild>2.1.0.0</zeusbuild>
<updatepoint>
<url>http://localhost:42349/z/bot.exe</url>
</updatepoint>
<droppoint>
<url>http://localhost:42349/z/gate.php</url>
</droppoint>
<webdatafilters>
<url><![CDATA[!*.microsoft.com/*]]></url>
<url><![CDATA[!http://*myspace.com*]]></url>
<url><![CDATA[https://www.gruposantander.es/*]]></url>
<url><![CDATA[!http://*odnoklassniki.ru/*]]></url>
<url><![CDATA[!http://vkontakte.ru/*]]></url>
<url><![CDATA[@*/login.osmp.ru/*]]></url>
<url><![CDATA[@*/atl.osmp.ru/*]]></url>
<url><![CDATA[!*.facebook.com/*]]></url>
</webdatafilters>
</root>
The targets list appear to be quite standard and probably not manually configured. Nevertheless, the ZeuS bot will collect and report all HTTP credentials it can, without requiring specific configuration entries.
Bitcoin Mining
“My guess is that around 30% of the whole bitcoin hashing power come from botnets, the amount coming from "unknown" pools.”
- throwaway236236
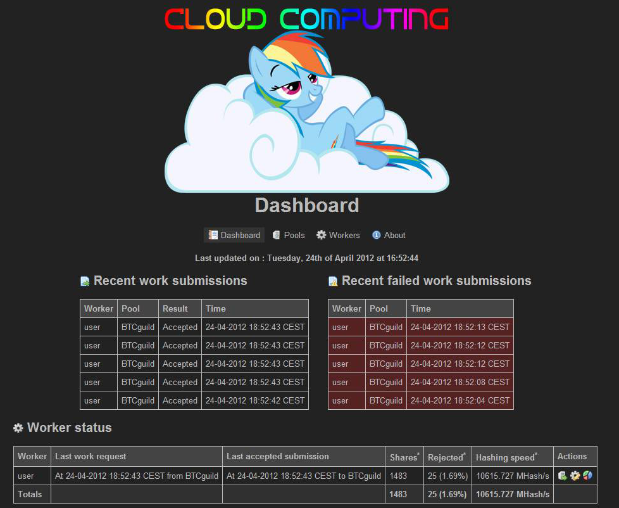
The malware embeds the “CGMiner” open-source bitcoin miner, which supports both GPU as well as regular CPU mining. Skynet installs a WH_MOUSE and a WH_KEYBOARD hook procedures that monitor the systems for keystrokes or mouse movements. By doing so it's able to understand whether the victim is interacting with the desktop and, in order to be less noticeable, it starts mining bitcoins only after two minutes of inactivity and immediately stops when some monitored event occurs.
As a matter of fact, the operator appears concerned with not affecting his victims' recreation and entertainment:
“My Botnet only mines if the computer is unused for 2 minutes and if the owner gets back it stops mining immidiatly, so it doesn't suck your fps at MW3. Also it mines as low priority so movies don't lag. I also set up a very safe threshold, the cards work at around 60% so they don't get overheated and the fans don't spin as crazy.”
- throwaway236236
The individual miners request a work task from one of several web servers run by the botnet operators. These webservers host an open source application called “Bitcoin Mining Proxy”, which is used to centrally manage the distributed workers and assign pools to the miners.
The operator also provided a screenshot of his Bitcoin Mining Proxy control panel:
Following is the list of Bitcoin Mining Proxy servers we identified being used by the botnet:
95.211.7.6:81
109.236.80.74:81
77.235.61.37:81
74.91.20.82:81
74.82.212.213:81
88.191.123.223:81
178.33.32.238:81
At the time of writing only the first two appear to be active.
Tracking the Botnet
My momma always said, "A botnet is like a box of chocolates. You never know what you're gonna get."
- throwaway236236
While reverse engineering the malware sample we were able to identify the Tor Hidden Service it was connecting to in order to receive its commands through its IRC Command & Control.
At the time of writing the IRC server is still running at the domain uy5t7cus7dptkchs.onion on port 16667. Once connected, the bot joins the channels #5net1 and #allin. The botnet seems to be still very active and maintained, in fact even during the few days we've been monitoring it, we observed it conducting some DDoS attacks. Following are some logs showing the botnet operator instructing all the bots to perform a SYN Flooding DDoS attack against an IP address (that we partially censored) on port 111.
02:48 < sudo> !syn 31.204.xxx.xxx 111 1 10
02:52 < sudo> !syn 31.204.xxx.xxx 111 1 30
03:47 -!- mode/#allin [+o sudo] by sudo
03:48 -!- sudo changed the topic of #allin to: !silence on
03:48 < sudo> !silence on
05:29 < sudo> !syn 31.204.xxx.xxx 111 1 10
05:56 < sudo> !syn 31.204.xxx.xxx 111 1 15^
05:56 < sudo> !syn 31.204.xxx.xxx 111 1 15
05:58 < sudo> !syn 31.204.xxx.xxx 111 1 15
05:59 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:00 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:08 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:29 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:56 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:58 < sudo> !syn 31.204.xxx.xxx 111 1 15
06:58 < sudo> !syn 31.204.xxx.xxx 111 1 15
The target of the attack was a server located in The Netherlands. We informed and cooperated with the affected organization, which kindly provided us with the list of IP addresses blocked by their firewalls during the ongoing attacks.
Following are some maps representing the geographical location of the attacking hosts.
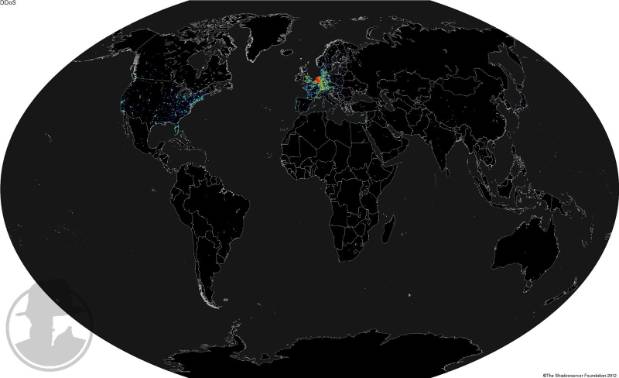
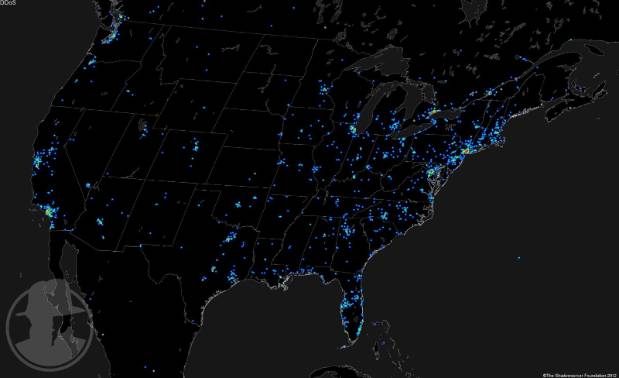
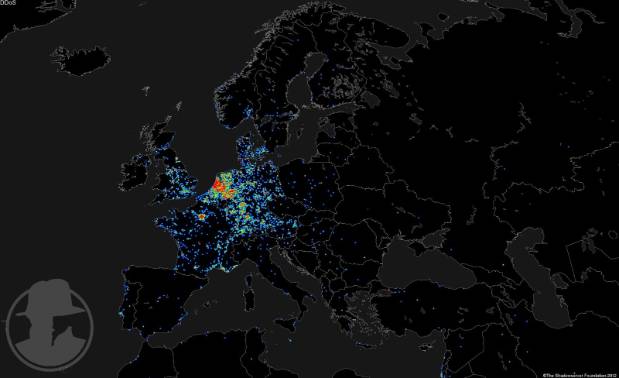
It's interesting to note that the highest concentration of bots are located in central Europe, with high densities in The Netherlands and Germany. We believe the size of the botnet amounts to between 12 and 15 thousand compromised computers.
Monetization
“Botnet operation is a mini job, once a day you check for 30minutes, pay once a month server bills, sell for about an hour information on the market and enchance your code if you feel like it. I was thinking about working for Kaspersky, but these guys want all kinds of phony diplomas and can't even recognize native code (see the duqu 'incident'). The profit? Depends, sometimes 400$ a day, sometimes none, but a steady 40$ a day with bitcoins alone.”
- throwaway236236
As kindly explained by Mr. Throwaway, the main source of monetization comes from both the Bitcoin mining as well as the credentials harvested by ZeuS. He also explained that he doesn't cash out the stolen accounts himself, but rather sells them on the black market, which is convenient and much less risky.
Conclusions
The way we encountered this malware was completely incidental and we had some good fun reversing and analyzing it. Despite not being particularly sophisticated it represents a nice example of a simple but still effective botnet with a large portfolio of capabilities.
The most important factor is certainly the adoption of Tor as the main communication channel and the use of Hidden Services for protecting the backend infrastructure. While it's surprising that not more botnets adopt the same design, we can likely expect more to follow the lead in the future.
Another surprising factor is that while the Reddit post was widely covered more than 6 months ago, the botnet went apparently (at least to the public) unnoticed until now. It will be interesting to follow its evolution and find out if there's any realistic way to dismantle it.
The lessons learned are:
- Exploitation is not required to build a decently-sized botnet. Always be careful when using any Internet service, especially file sharing.
- It is possible to build an almost cost-free bulletproof botnet. In its democratic nature Tor is a great tool, both for legitimate users as well as for cybercriminals unfortunately.
Lesson for botnet operators:
- As The Grugq says, “keep your mouth shut”. Talking about your business on Reddit is not such a smart idea.
This analysis was conducted by Claudio “nex” Guarnieri and Mark “rep” Schloesser, Security Researchers at Rapid7.
Credits
Thanks to the friend Pallav Khandhar for helping with the analysis of the ZeuS binary.
Thanks to the Shadowserver fellow Dave DeCoster for creating the fancy maps.