Last updated at Mon, 24 Jul 2017 15:07:21 GMT
Introductions
After lurking for a little while, I'm starting to write on SecurityStreet today in order to introduce RiskRater, a tool we've been working on recently. RiskRater is an interactive free tool designed to give security professionals a quick snapshot of how they are doing in terms of their security controls for endpoints, mobile devices and user-based risk.
What Does RiskRater Do?
We frequently hear from security professionals that they are under constant pressure to keep up to date and are often under-resourced. As a result, they need to work hard to prioritize their actions for maximum efficiency and effectiveness. Thus, we created RiskRater to help identify the areas of a security program that need work and to give guidance about what can be done, as well as the importance of doing each of these things.
The tool aims to bring to your attention areas that need work in a prioritized order. Of all the tasks you could do to improve your organization's overall security, which should you do first? Some are more valuable to do before others, and RiskRater will help you identify what they are.
How Does RiskRater Work?
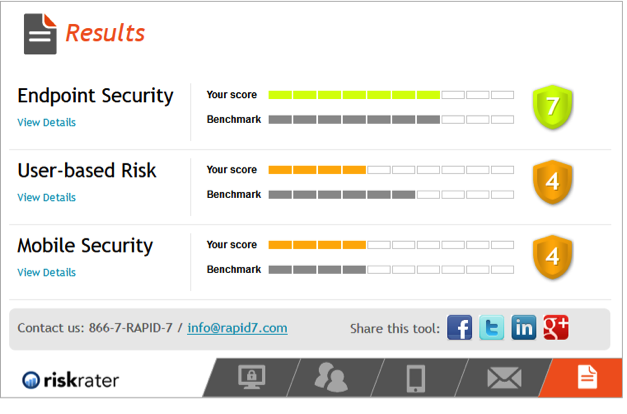
Essentially, RiskRater is a straightforward grading tool focused on security. It poses a number of questions for each of three categories (endpoint, mobile, and user), and calculates a score from 1-10 based on your answers. The scoring is determined using an algorithm we created, and then mapped against benchmarks for the three categories. We developed those benchmarks by working with data collected from our own research, as well as responses from over 600 organizations. Thank you very much to everyone who gave us feedback. We really wanted to create a baseline so users can see how they're doing compared to others, so we greatly appreciate the information you shared with us. As more people use the tool, the benchmarks will evolve to reflect the user base (but no specific or personal attributable information will be shared).
Calculating Risk
I worked on the risk calculation part of the project and want to explain how that works. The main RiskRater page tells you that RiskRater helps "you understand your endpoint, user and mobile risk and security posture, and gain practical advice on how you can strengthen your defenses" but it doesn't give any more detail than that, so here's a little more on how it works.
RiskRater uses a grading model to produce results. You supply answers to questions, it grades your answers and then it gives you results. The calculations we use in the RiskRater model aren't very complicated. Instead, we focus on creating good weights for each question. These weights are derived from a mixture of personal experience and expertise gathered from our in house security experts, (the Rapid7 Labs team and Metasploit researchers), from published guidance, and from insight and analysis of our customer's security practices.
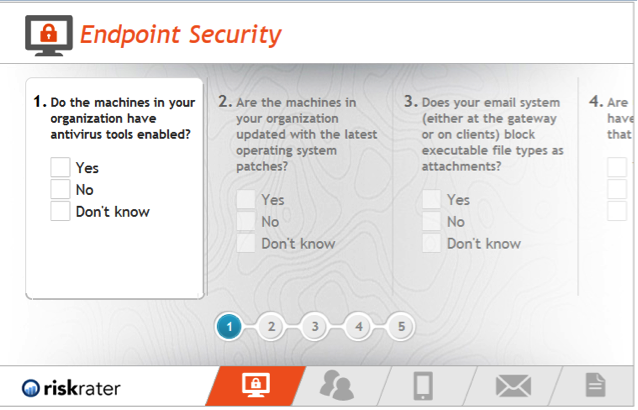
If you answer "yes" to all the questions you'll get a 10 (out of 10). If you answer "no" or "don't know" to all the questions, you'll get a 1. More specifically, each of the questions to which you answer "yes" contributes a certain amount to your scores, and these amounts are what determine the guidance RiskRater gives.
Not every action you take to improve your security has the same value. For instance, our research shows that in general, keeping commonly exploited applications and operating systems up to date is more valuable than preventing data from being copied to or from USB thumb drives. Which isn't to say that restricting data transfer to and from USB thumb drives isn't worthwhile, just that if you need to do decide which problem to address first, we recommend making sure everything is updated.
We have tried to encode our knowledge of the varying importance of different security measures into RiskRater, by having different questions have different values, so it can give you useful guidance.
Give it a go
Answering the questions RiskRater asks only takes a few minutes and you'll see your scores right away as soon as you're done. So go try RiskRater for yourself, and if you have any questions or feedback, please let us know in the comments section below.
