Last updated at Fri, 07 Jul 2023 14:57:05 GMT
I've been in love with the idea of a SIEM since I was a system administrator. My first Real Job™ was helping run a Linux-based network for a public university. We were open source nuts, and this network was our playground. Things did not always work as intended. Servers crashed, performance was occasionally iffy on the fileserver and the network, and we were often responding to outages.
Of course, we had tools to alert us when outages were going on. I learned to browse the logs and the system monitors, and soon got to a point where I could predict (with varying degrees of success) when a full blown crash was coming. I was in operations, and I had no idea what a SIEM was, but I was all aboard the idea of logging, measuring, and detecting variations in my environment.
The operations challenges translate surprisingly well to the security space. The major difference is that in security, the difficulty ramps because we're dealing with problems that are actively trying not to be found. They're either trying very hard not to be logged, or they're trying very hard to not be detected when they are logged. I never had to worry about the fileserver hiding the impending crash from me.
SIEM tools do a fantastic job of aggregating logs, but as with ops logging, we need to add more to them to make sense of the data. Let's examine common evasion techniques attackers use to keep the SIEM alerts to a minimum.
Avoid Getting Logged
SIEMs are intended to log as much data as possible in order to assist with incident detection, response, and investigation. One challenge is that it can be prohibitive, either from a cost or storage perspective, to log everything. This is particularly true for the logs on all of the endpoints in an environment. Therefore, the best way to evade a SIEM security is to use tactics that are unlikely to be logged at all.
1. Social Engineering Remains King.
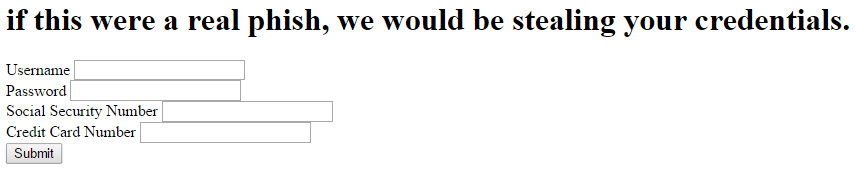
There aren't many better ways to get a foothold on a network than to have the users let you in. Social engineering is great for stealing credentials and getting shells. This can be done through malware, but it often simply involves convincing the user to type their password into a web form. Going straight for the credentials has the added benefit of not showing up in logs, well, anywhere. Even with malware, it's nearly trivial to write an attack package that will avoid antivirus, and VirusTotal gives attackers an easy medium through which to verify this. A meterpreter shell in particular isn't getting logged anywhere, and in most cases the outbound connections from a workstation are neither filtered nor tracked.
2. Stay Local. Once a foothold on a particular system is established, one of the most effective methods to move around unseen is to leverage local credentials. Many organizations leverage local administrator credentials that work across the environment. Unless they're watching the logs on every endpoint, local authentications aren't logged centrally and won't be seen. An attacker can take their time and move merrily from system to system, seeking out valuable information or more powerful network credentials at their own pace.
3. Play in the Cloud. Many organizations have limited visibility into cloud services. Valuable information can often be found in services like Office 365, Salesforce, and Box.com. A SIEM that's logging authentication attempts and security tools inside the perimeter often isn't covering cloud services. Stolen credentials, either from the aforementioned social engineering campaigns or from another source, can be re-used with ease against cloud services. Here an attacker can try to find further pivot points into the main infrastructure or cash out on the data they have immediate access to.
Avoid Getting Detected
While not getting logged is a lovely ideal, eventually an attacker will have to start making some kind of noise that gets logged where a SIEM can see it. They then run the risk of being caught by the various rules and detections that organizations configure in their SIEM. Detecting activity that varies from the baseline or starts stepping outside of its normal boundaries is powerfully dangerous for the attacker, and is the reason most companies employ a SIEM in the first place. Thankfully (?) there are a variety of tactics and techniques that can minimize the number of alerts generated, or avoid triggering them altogether.
4. Leverage Service Accounts. Service accounts are a particularly juicy target for an intruder. The beautiful thing about service accounts is that attackers can often just sit and wait for them to drop in their lap. A compromised system, whether it be a workstation or server, is likely to have some kind of service account log into it at some point, given enough time. Examples? Vulnerability scanners. Patch management systems. Software deployment. Many of these are operated using service accounts with passwords that never change… and have access to the entire network. It's a simple thing to wait for a service account authentication and steal either the token, hash, or cleartext password using something like mimikatz or incognito, and then move around the network. After all, there's nothing suspicious about an account whose normal activity is to sweep through the network.
5. Low and Slow.
When on a monitored network, an attacker's best bet after getting an initial foothold on a compromised system is to take a breath. Start looking at the network traffic coming to and from the system. Which systems are common targets? Which accounts are logging in and out? Which ones log in locally versus remotely? For example, the primary user of a particular compromised workstation might normally connect to a fileserver and a small group of shared workstations. These are the next logical stepping stones for the attacker. Evading a SIEM is as simple as not making any waves. When an account is seen moving to another system, follow it. Most SIEMs will have a great deal of trouble detecting an attacker that follows the same traffic patterns as the users and systems of the networks they compromise.
These techniques are used by attackers and penetration testers alike to avoid detection. SIEMs are great at aggregating data from a ton of sources, but without a significant cost and effort investment, most have major gaps in either the logging or the detection portion of the job.
At Rapid7, we've taken our knowledge of the attacker from the Metasploit project and our Global Services into our User Behavior Analytics solution, UserInsight. UserInsight fills the gaps in SIEM coverage to help detect stealthy attacks, accelerate investigations with user context, and expose risky user behavior from endpoint to cloud. To learn more, check out our 5-minute video, or request a free guided demo!