Last updated at Tue, 16 Jan 2024 16:12:05 GMT
It's been a long road to 4.0. The first 3.0 release was almost 5 years ago and the first release under the Rapid7 banner was almost 2 years ago. Since then, Metasploit has really spread its wings. When 3.0 was released, it was under a EULA-like license with specific restrictions against using it in commercial products. Over time, the reasons for that decision became less important and the need for more flexibility came to the fore; in 2008, we released Metasploit 3.2 under a 3-clause BSD license. Licensing is definitely not the only place Metasploit's fexibility has increased. Over the last 5 years, we've added support for myriad exploitation techniques, network protocols, automation capabilities, and even user interfaces. The venerable msfweb is gone along with the old gtk-based msfgui. Taking their place are the newer java-based msfgui and armitage, both of which have improved by leaps and bounds since their respective introductions.
Five years ago, every exploitation tool out there was focused on running an exploit and getting a shell (usually a crappy cmd.exe shell, at that). Today, Metasploit encompasses every aspect of a penetration test. Dozens of auxiliary modules assist with reconnaisance, more than two hundred others help with information gathering and discovery; hundreds of exploits get you a toe-hold on the network; and the newest addition to the module family, post modules, help simplify and automate increasing your access. All of the data you gather can be stored in a database. For high-quality reporting and even greater automation, Metasploit Pro rounds out an engagement. Five years ago, Metasploit had already come a long way in making exploit development easier but the widespread adoption of DEP and ASLR has pushed the project even further toward accelerating what has now become a much more difficult process.
All of that leads us to the Metasploit Framework version 4.0, released today.
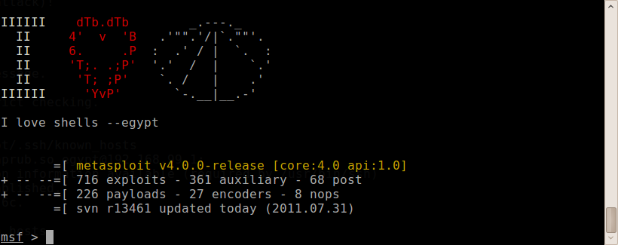
To make the awesomeness of 4.0 stand out visually from its predecessors, we've built an array of stunning new ASCII art banners. My favorite, of course, is this one:
In addition to the visual differences, Metasploit Framework 4.0 comes with an abundance of new features and bug fixes. Contributor TheLightCosine continues with his onslaught of password-stealing post modules and another contributor, Silent Dream, has begun helping out in that arena as well. Other post modules have seen considerable improvement and expansion thanks to Carlos Perez. The recent Exploit Bounty netted a total of six new exploit modules, and other development added another 14 since the last release.
Adding to Metasploit's extensive payload support, Windows and Java Meterpreter now both support staging over http and Windows can use https. In a similar vein, POSIX Meterpreter is seeing some new development again. The last developer left it with little documentation on how to build it, so getting it to compile was a hurdle that we put off for too long. Now that it compiles, you can expect a more flexible payload for Linux. It still isn't perfect nor is it nearly as complete as the windows version, but many features already work.
Another flexibility improvement comes in the form of a consolidated pcap interface. The pcaprub extension ships with the Linux installers as of this release and support for Windows will come soon. Modules that used Racket for generating raw packets have been converted to Packetfu, which provides a smoother API for modules to capture and inject packets. As always, you can get the latest version from http://www.metasploit.com/download/ and full details of this release can be found in the Release Notes.
Everyone on the Metasploit team is proud of the first major version bump in half a decade. May it bring you many shells.